Embracing Remote Work With The Right Technology

Embracing Remote Work With The Right Technology
Whether you’ve accepted it at your business or not, remote work is only going to grow and become a necessity for businesses to offer partial or full remote. However, moving to an increased remote workforce should not be a scary proposition. If you make it easy for yourself and your employees, it will improve your business.
If you currently offer remote work or looking at potentially expanding this option, there are a few key items to consider. Let’s lay out the most important aspects:
Hardware, access and security
Hardware
User’s computers should be laptop or Desktop at work AND home.
Allowing personal devices opens your organization to risk that can easily avoidable. For desktop, it’s easy: identical setup at your business and at their home.
For laptop, here is the perfect setup:
- Powerful laptop
- USB docking station – these are easier and more compatible than the old school docking stations
- Dual monitors – now you can even have 3 monitors!
That’s it! Simple and easy. They unplug their laptop and connect the USB port and are instantly running at home.
**VoIP Phones: This is listed under hardware, but physical phones are quickly becoming obsolete. Download the included software phone and provide an inexpensive headset for your employees so they can easily take their work phone with them on their computer!
Access
There are lots of ways to make access easy without sacrificing security. Having your employees connect to the office through a physical server is the “old school” method that many businesses are still utilising. Consider moving to SharePoint.
With SharePoint, folders can sync to the file explorer, so it looks just like what they’re used to! That data is then backed up, just like a server would be.

However, you may have business specific applications that are not cloud-based and require a server. These are becoming rarer but may still be applicable. We don’t want to get too technical, so you can reach out and we can provide an audit on the best solution for accessibility.
Moving to a hosted (cloud) solution or ensuring remote access for your users to your server onsite would be the primarily recommendations here.
Security
As mentioned, you don’t want users accessing company data on their personal devices. There are very easy force functions your IT provider can implement to ensure this is not occurring.
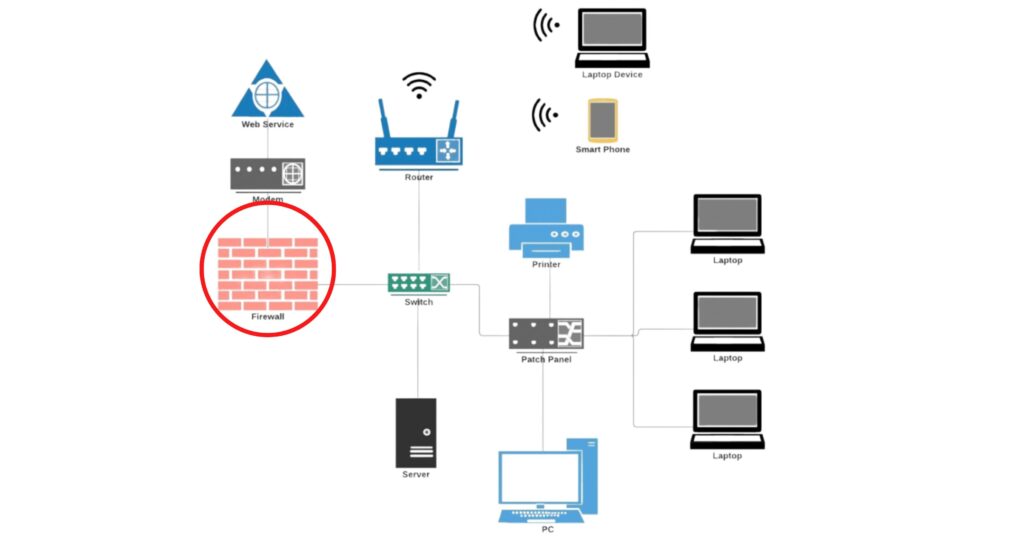
As more devices move away from the umbrella of the firewall (a firewall is a physical device on your network that “filters” your internet data and protects computers at your business) you will need to ensure your security is focused on the computer and laptop, rather than the office location.
Okay, we hope we didn’t lose you here. Here is a quick infographic explaining what I mean:
Embracing remote work with the right technology
How do we improve the computer/laptop security?
There’s a lot that we do, and I’m sure your current provider may do too. Here is a quick summary of the highest benefit lowest impact layers you need to have in place:
- Multi-factor authentication – when the users log into their Microsoft accounts, they will be prompted with a push notification to their mobile device confirming it’s them. This prevents 99% of personal identity attacks… it’s a no-brainer!
Anti-Virus – There are lots of terms for this, but at the end of the day you need a trusted anti-virus on all computers.
Conditional Access Policies – you want to make sure company data is NOT accessed on personal devices. Get your IT team to set this policy up and you’re all set
- Managed Detection and Response – This is the one all of those cybersecurity insurance questionnaires ask about. Make sure your provider has this on ALL machines.
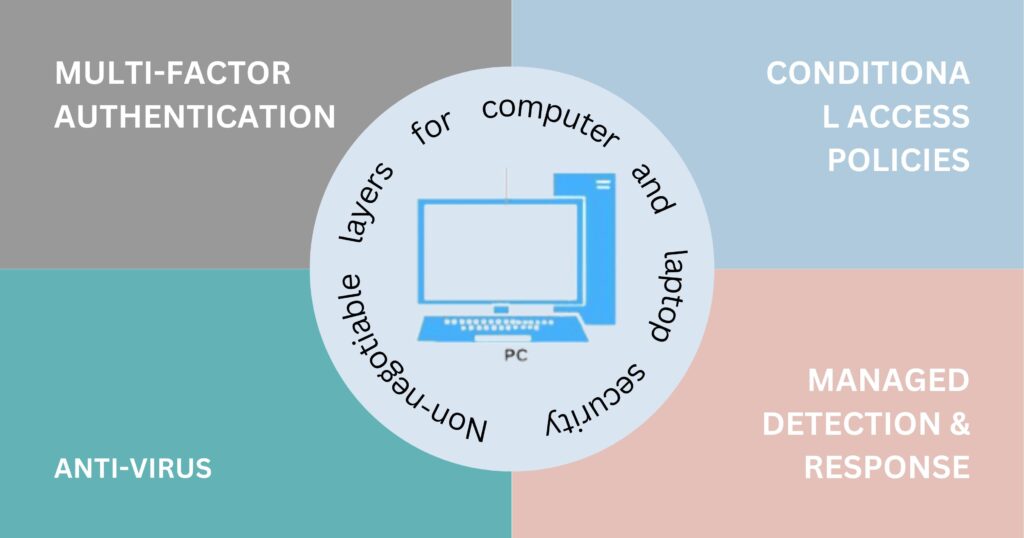
There are more layers to consider, but these are the non-negotiables.
Lastly, ensure employees have strong KPIs and that you have an IT team with ample experience in consulting and implementing these types of setups.
Do you need help implementing systems so your team can work remotely?
Share This Post
Subscribe To Our Newsletter
More To Explore
Cybersecurity
Eye-opening Insights from the 2023 Annual Cybersecurity Attitudes and Behaviors Report
We are living in an era dominated by digital connectivity. You can’t overstate the importance of cybersecurity. As technology advances, so do the threats that
April 20, 2024

Cybersecurity
Be Careful When Scanning QR Codes – There’s a New Scam Going Around!
QR codes are everywhere these days. You can find them on restaurant menus, flyers, and posters. They’re used both offline and online. QR codes are
April 15, 2024
